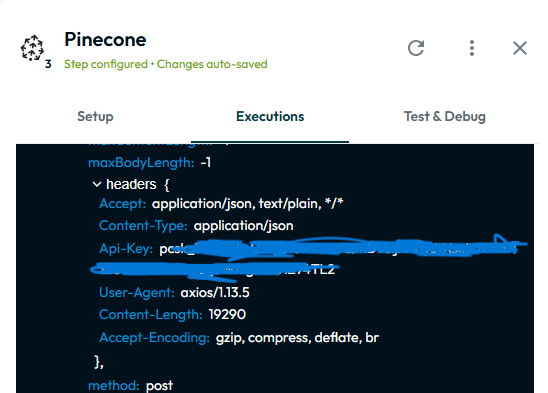
The Pinecone API key is displayed in plain text within execution debug logs when running a Pinecone query step. Sensitive credentials should be masked or redacted, but the full API key appears in request headers during log inspection. This creates a potential security risk, especially in shared workspaces or when logs are exported or reviewed by multiple users, and does not align with common security best practices.
Media:
Steps to Reproduce:
-
Configure a Pinecone query step with an API key.
-
Execute the workflow.
-
Open the execution/debug logs.
-
Inspect the request headers.
Expected Result:
API keys and other sensitive headers (e.g., Api-Key) should be masked or redacted in logs (for example: pcsk_****abcd) and never displayed in full.
Actual Result:
The full Pinecone API key is visible in plain text within the execution debug logs when inspecting the HTTP request.